Cybersecurity Online Test
For jobseekers
Practice your skills and earn a certificate of achievement when you score in the top 25%.
Take a Practice TestFor companies
Screen real Cybersecurity skills, flag human or AI assistance, and interview the right people.
About the test
The Cybersecurity online test assesses knowledge of web application and network security to prevent unauthorized access and misuse of resources.
The assessment includes work-sample tasks such as:
- Managing authorization and controlling access rights.
- Encrypting and decrypting information.
- Testing security to prevent malicious attacks.
A good cybersecurity specialist should know how to find security flaws in an application or network and be familiar with common methods of attack, such as SQL injection, XSS, and CSRF, in order to protect valuable data.
Sample public questions
A web application for ordering cat food charges users and places an order when an HTTP GET request is issued to the following URL:
http://www.catsupplies.com/order?brand=xxxxx&quantity=xxxxx
A malicious website could add snippets like this to their site:
<img src="http://www.catsupplies.com/order?brand=xxxxx&quantity=xxxxx">What would help protect against such attacks, considering that the web application has the CORS policy that only allows requests from the same site?
Employees of a company are facing lots of bounced email notifications from email addresses they have never sent messages to. Select the options below which are correct for the given scenario.
For jobseekers: get certified
Earn a free certificate by achieving top 25% on the Cybersecurity test with public questions.
Take a Certification TestSample silver certificate
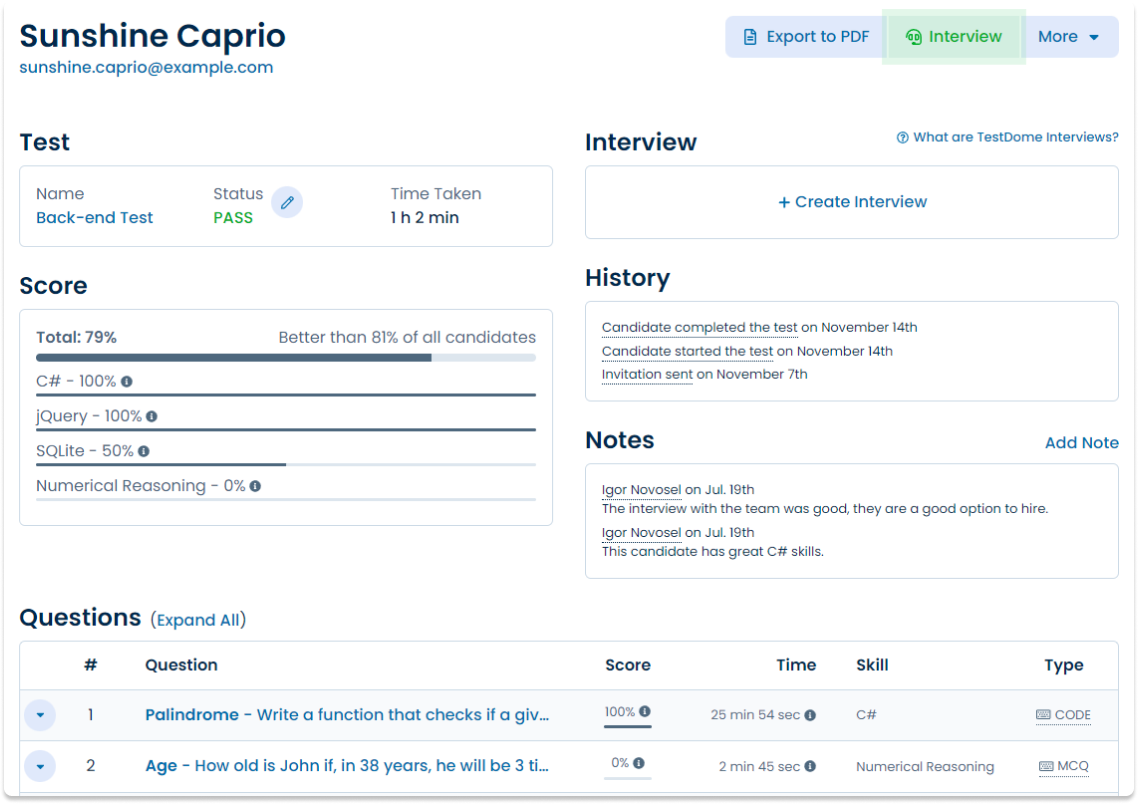
Sunshine Caprio
Java and SQL TestDomeCertificate
For companies: premium questions
Buy TestDome to access premium questions that can't be practiced.
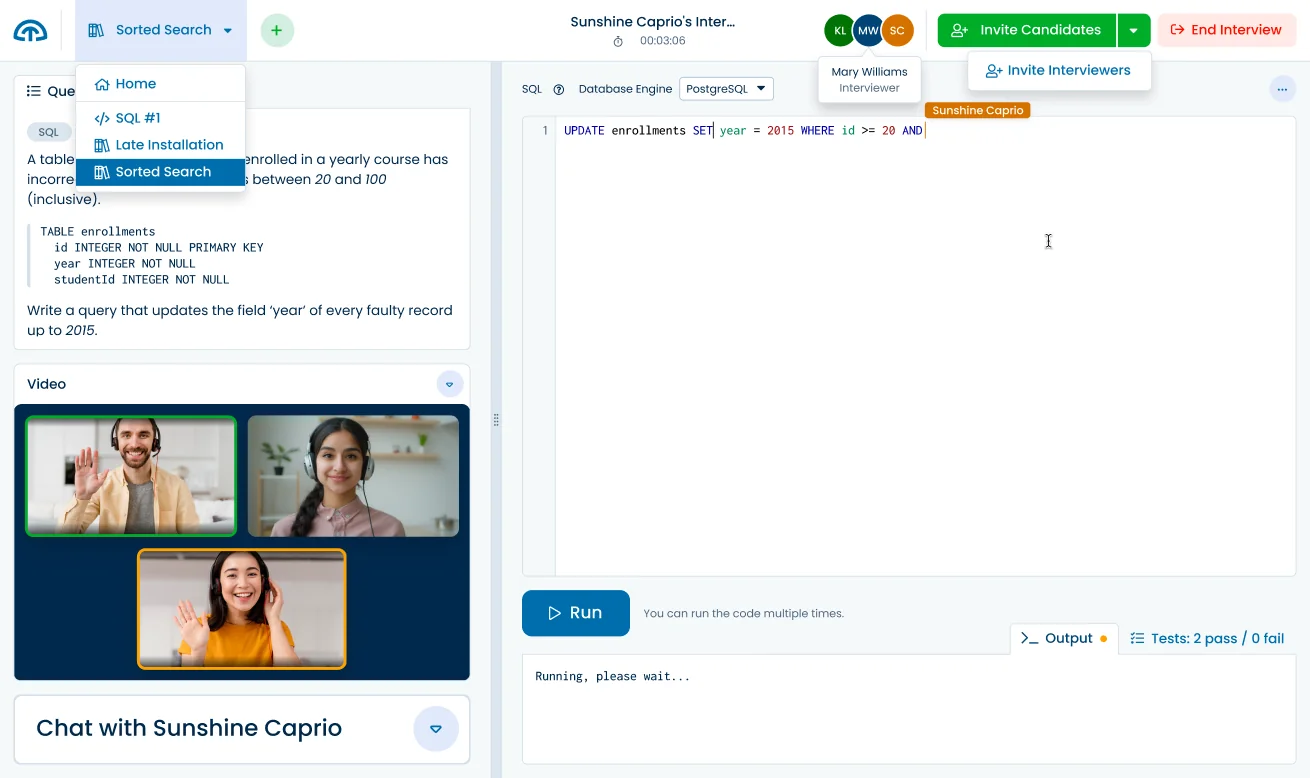
Ready to interview?
Use these and other questions from our library with our
Code Interview Platform.
23 more premium Cybersecurity questions
IP Assignment, Network Hops, Routing Table, Introducing NAT, Web Vulnerabilities, Web Security, Stock Data, Umbrella Store, Furniture Manufacturer, Network Permissions, Transport Layer Security, Connecting to a Switch, DNS Zone, Intranet Access, Introducing DHCP Server, Health Insurer, IP Address, Load Distribution, DNS Lookup, Private Subnet, Company Subnet, User Search, Report XSS.
Skills and topics tested
- Network Administration
- Application Layer
- IP
- Network Layer
- Routing
- Routing Table
- NAT
- Firewall
- Network Security
- Web Application Security
- Encryption
- CSRF
- Authorization
- Access Control List
- Subnet
- Presentation Layer
- Protocol
- Data Link Layer
- Network Switch
- DNS
- Multi-Factor Authentication
- VPN
- DHCP
- Password Storage
- Load Balancing
- Security Testing
- SQL Injection
- XSS
For job roles
- Cybersecurity analyst
- Information security analyst
- Network Administrator
- System Administrator (Sysadmin)
Sample candidate report
Need it fast? AI-crafted tests for your job role
TestDome generates custom tests tailored to the specific skills you need for your job role.
Sign up now to try it out and see how AI can streamline your hiring process!
What others say
Simple, straight-forward technical testing
TestDome is simple, provides a reasonable (though not extensive) battery of tests to choose from, and doesn't take the candidate an inordinate amount of time. It also simulates working pressure with the time limits.
Jan Opperman, Grindrod Bank
Product reviews
Used by
Solve all your skill testing needs
150+ Pre-made tests
130+ skills
AI-ready assessments
How TestDome works
Choose a pre-made test
or create a custom test
Invite candidates via
email, URL, or your ATS
Candidates take
a test remotely
Sort candidates and
get individual reports